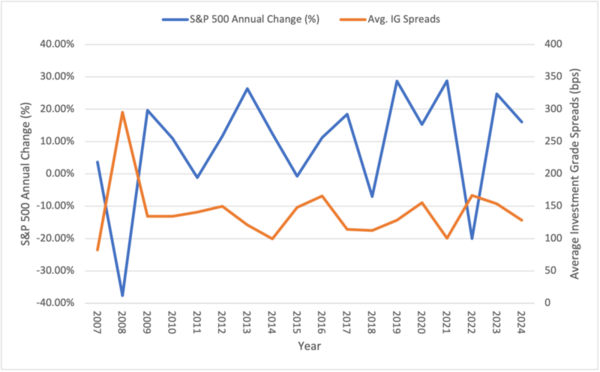
The authors examined the relationships between S&P 500 Technology and Financials equity sectors and their corresponding investment-grade fixed-income markets from 1995 to 2025.
Read More...Sector Dynamics: Equity and fixed-income performance across market cycles
The authors examined the relationships between S&P 500 Technology and Financials equity sectors and their corresponding investment-grade fixed-income markets from 1995 to 2025.
Read More...Artificial intelligence face-tracking for a semi-virtual reality gaming experience

The authors studied the impact of AI face-tracking technology on the immersiveness of videogames as an alternative to virtual reality gaming.
Read More...Identifying the wavelength that generates the most voltage and current in a solar panel
.jpg)
A key barrier to adoption of solar energy technology is the low efficiency of solar cells converting solar energy into electricity. Sims and Sims tackle this problem by coding a Raspberry Pi as a multimeter to determine which wavelength of light generates the most voltage and current from a solar panel.
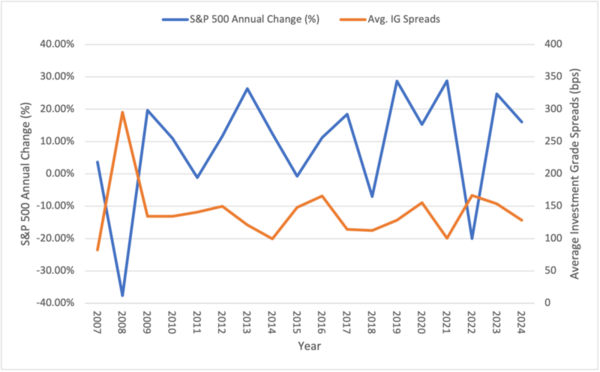
Read More...The Effect of Delivery Method, Speaker Demographics, and Physical Environment on the Engagement Level of Older Adults
With an increasing older adult population and rapid advancements in technology, it is important that senior citizens learn to use new technologies to remain active in society. A variety of factors on learning were investigated through surveys of senior citizens. Older adults preferred an interactive lesson style, which also seemed to help them retain more course material.
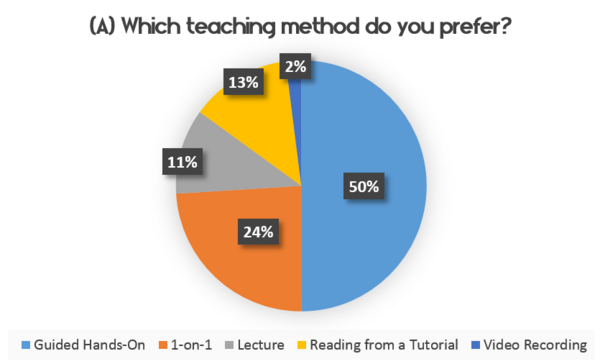
Read More...Enhancing marine debris identification with convolutional neural networks
Plastic pollution in the ocean is a major global concern. Remotely Operated Vehicles (ROVs) have promise for removing debris from the ocean, but more research is needed to achieve full effectiveness of the ROV technology. Wahlig and Gonzales tackle this issue by developing a deep learning model to distinguish trash from the environment in ROV images.
Read More...The effects of social media on STEM identity in adolescent girls

Social media is widely used and easily accessible for adolescents, it has the potential to increase STEM (Science, Technology, Engineering, and Math) identity in girls. We aimed to investigate the effects of exposure to counter-stereotypical portrayals of women in STEM on social media on the STEM identity of adolescent girls. The study concluded that social media alone may not be an effective tool to increase STEM identity in girls. Social media can still be used as a complementary tool to support and encourage women in STEM, but it should not be relied upon solely to address the gender disparity in STEM fields.
Read More...Artificial intelligence assisted violin performance learning
In this study the authors looked at the ability of artificial intelligence to detect tempo, rhythm, and intonation of a piece played on violin. Technology such as this would allow for students to practice and get feedback without the need of a teacher.
Read More...Can the Growth Mindset Encourage Girls to Pursue “Male” Careers?

Despite major advances in gender equality, men still far outnumber women in science, technology, engineering and math (STEM) professions. The purpose of this project was to determine whether mindset could affect a student’s future career choices and whether this effect differed based on gender. When looking within the gender groups, 86% of females who had a growth mindset were likely to consider a “male” career, whereas only 16% of females with fixed mindset would likely to consider a “male” career. Especially for girls, cultivating a growth mindset may be a great strategy to address the problem of fewer girls picking STEM careers.
Read More...A Cloud-Enabled Communication Strategy for Wildfire Alerts
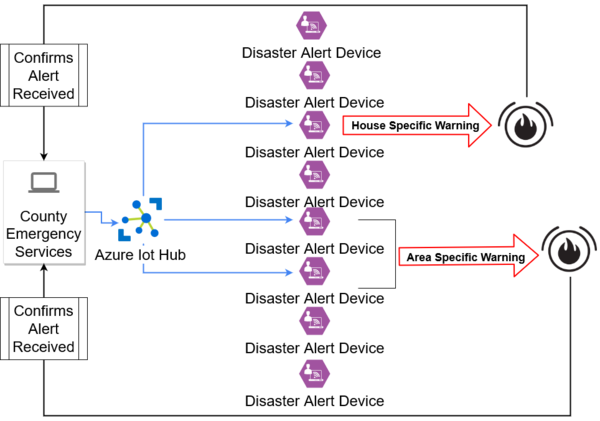
The traditional alert system in California consists of Wireless Emergency Alerts (WEAs), which lack location specificity, and sign-up-based technology which is limited by the number of sign ups. Those who do not have phones or have a silence option on their devices are most at risk from the current alert system. Here the authors developed cloud-enabled crisis connection for disaster alerts (CRISIS-CONNECT) to mitigate problems associated with the current alert system.
Read More...Assessing Attitude Across Different Age Groups in Regard to Global Issues: Are Kids More Optimistic Than Adults?

In this article the authors investigate whether there is a correlation between age of a person and their outlook on global issues such as technology, politics, and environment. They find a correlation between increased age and decreased optimism. However regardless of age, they find that respondents believe certain characteristics such as technology and willingness to change are essential for improvements.
Read More...