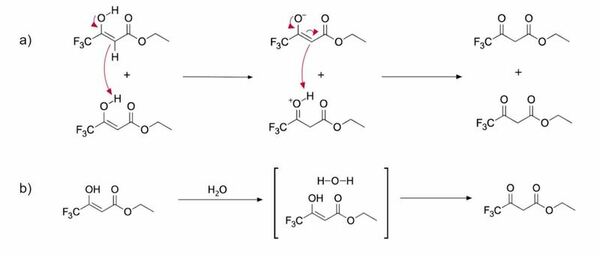
In this study, the authors determined whether tautomerization dynamics in protic and aprotic solvents displayed differences in reaction rates and in the proportion of the keto and enol tautomers present.
Read More...Deuterated solvent effects in the kinetics and thermodynamics of keto-enol tautomerization of ETFAA
In this study, the authors determined whether tautomerization dynamics in protic and aprotic solvents displayed differences in reaction rates and in the proportion of the keto and enol tautomers present.
Read More...A novel filtration model for microplastics using natural oils and its application to the environment

Recognizing the need for a method to filter microplastics from polluted water the authors sought to use nonpolar solvents, palm oil and palm kernel oil, to filter microplastics out of model seawater. By relying on the separation of polar and nonpolar solvents followed by freezing the nonpolar solvent, they reported that microplastics could be extracted with percentages ranging from 96.2% to 94.2%. They also provided an estimation to use this method as part of container ships to clean the Pacific Ocean of microplastics.
Read More...Impacts of COVID-19 on daily water use: Have people started using more water?

In this study, the authors investigated whether water usage changed in São Paulo during the COVID-19 quarantine and explored reasons why.
Read More...Modelling effects of alkylamines on sea salt aerosols using the Extended Aerosols and Inorganics Model

With monitoring of climate change and the evolving properties of the atmosphere more critical than ever, the authors of this study take sea salt aerosols into consideration. These sea salt aerosols, sourced from the bubbles found at the surface of the sea, serve as cloud condensation nuclei (CCN) and are effective for the formation of clouds, light scattering in the atmosphere, and cooling of the climate. With amines being involved in the process of CCN formation, the authors explore the effects of alkylamines on the properties of sea salt aerosols and their potential relevance to climate change.
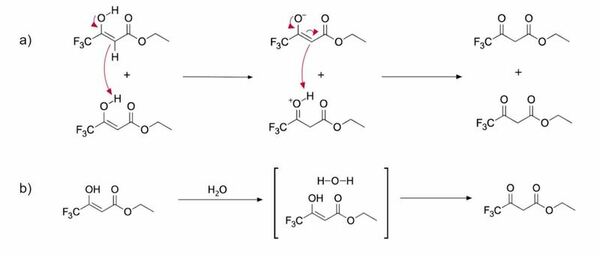
Read More...Lack of correlation between odor composition and neuron response in the olfactory cortex of mice
To address whether odor sensory circuits are organized topographically, the authors investigate whether the neuronal responses to similar odors amongst different mice mapped similarly in brain.
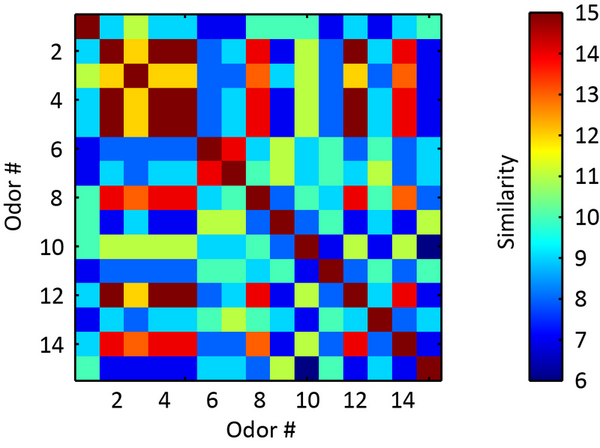
Read More...Investigating Hydrogen as a Potential Alternative to Kerosene in Fueling Commercial Aircraft
Growing climate concerns have intensified research into zero-emission transportation fuels, notably hydrogen. Hydrogen is considered a clean fuel because its only major by-product is water. This project analyzes how hydrogen compares to kerosene as a commercial aircraft fuel with respect to cost, CO2 emissions, and flight range.
Read More...A novel bioreactor system to purify contaminated runoff water
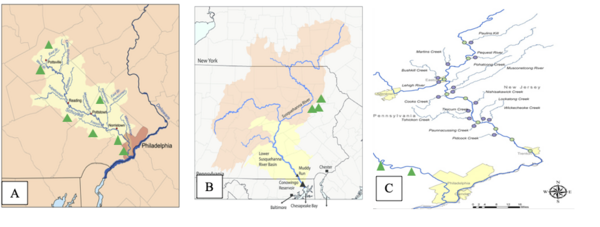
In this study, the authors engineer a cost-effective and bio-friendly water purification system using limestone, denitrifying bacteria, and sulfate-reducing bacteria. They evaluated its efficacy with samples from Eastern PA industrial sites.
Read More...Effects of Prolonged Azithromycin Therapy on Bacterial Resistance to Functionally Analogous Antibiotics
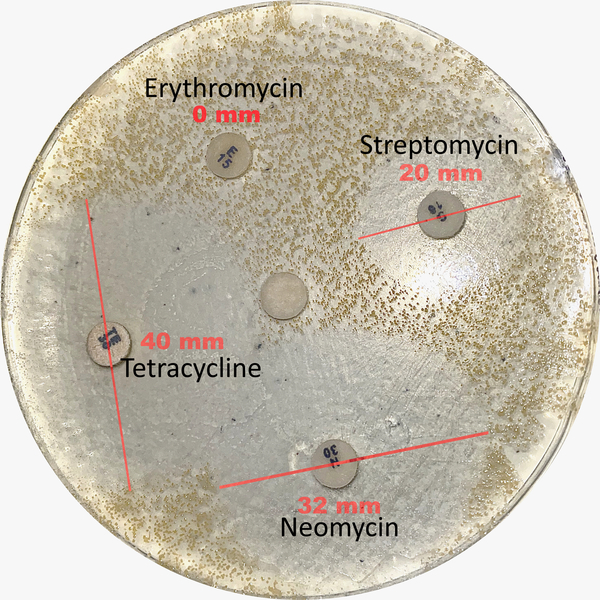
In this study, the authors investigate a potential case of cross antibiotic-resistance. Using swabs from an individual who received long-term treatments of azithromycin, they addressed the question of whether any bacteria in this individual might develop resistance to not only azithromycin, but also other antibiotics with similar structures. This study cleverly addresses the important issue of antibiotic resistance from a new and thoughtful approach.
Read More...Honey Bee Pollen in Allergic Rhinitis Healing

The most common atopic disease of the upper respiratory tract is allergic rhinitis. It is defined as a chronic inflammatory condition of nasal mucosa due to the effects of one or more allergens and is usually a long-term problem. The purpose of our study was to test the efficiency of apitherapy in allergic rhinitis healing by the application of honey bee pollen. Apitherapy is a branch of alternative medicine that uses honey bee products. Honey bee pollen can act as an allergen and cause new allergy attacks for those who suffer from allergic rhinitis. Conversely, we hoped to prove that smaller ingestion of honey bee pollen on a daily basis would desensitize participants to pollen and thus reduce the severity of allergic rhinitis.
Read More...Assessing and Improving Machine Learning Model Predictions of Polymer Glass Transition Temperatures
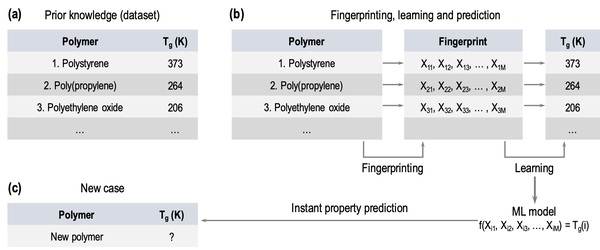
In this study, the authors test whether providing a larger dataset of glass transition temperatures (Tg) to train the machine-learning platform Polymer Genome would improve its accuracy. Polymer Genome is a machine learning based data-driven informatics platform for polymer property prediction and Tg is one property needed to design new polymers in silico. They found that training the model with their larger, curated dataset improved the algorithm's Tg, providing valuable improvements to this useful platform.
Read More...