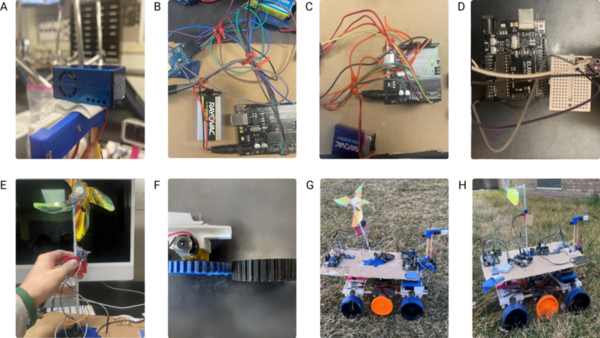
Pediatric asthma remains a significant health issue for Dallas students. This study examined the relationship between microclimatic parameters, vegetation, and pediatric asthma vulnerability (PAV) in urban schools.
Read More...Rover engineered to evaluate impacts of microclimatic parameters on pediatric asthma in Dallas schools
Pediatric asthma remains a significant health issue for Dallas students. This study examined the relationship between microclimatic parameters, vegetation, and pediatric asthma vulnerability (PAV) in urban schools.
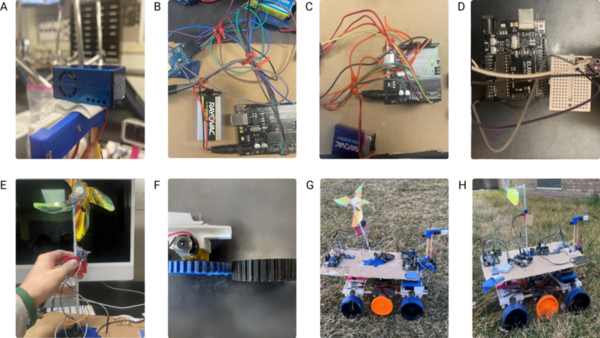
Read More...A meta-analysis on NIST post-quantum cryptographic primitive finalists
The advent of quantum computing will pose a substantial threat to the security of classical cryptographic methods, which could become vulnerable to quantum-based attacks. In response to this impending challenge, the field of post-quantum cryptography has emerged, aiming to develop algorithms that can withstand the computational power of quantum computers. This study addressed the pressing concern of classical cryptographic methods becoming vulnerable to quantum-based attacks due to the rise of quantum computing. The emergence of post-quantum cryptography has led to the development of new resistant algorithms. Our research focused on four quantum-resistant algorithms endorsed by America’s National Institute of Standards and Technology (NIST) in 2022: CRYSTALS-Kyber, CRYSTALS-Dilithium, FALCON, and SPHINCS+. This study evaluated the security, performance, and comparative attributes of the four algorithms, considering factors such as key size, encryption/decryption speed, and complexity. Comparative analyses against each other and existing quantum-resistant algorithms provided insights into the strengths and weaknesses of each program. This research explored potential applications and future directions in the realm of quantum-resistant cryptography. Our findings concluded that the NIST algorithms were substantially more effective and efficient compared to classical cryptographic algorithms. Ultimately, this work underscored the need to adapt cryptographic techniques in the face of advancing quantum computing capabilities, offering valuable insights for researchers and practitioners in the field. Implementing NIST-endorsed quantum-resistant algorithms substantially reduced the vulnerability of cryptographic systems to quantum-based attacks compared to classical cryptographic methods.
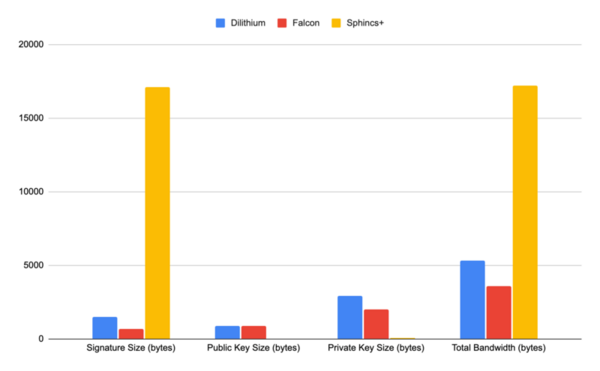
Read More...Cardiovascular Disease Prediction Using Supervised Ensemble Machine Learning and Shapley Values
The authors test the effectiveness of machine learning to predict onset of cardiovascular disease.
Read More...Bird Feeding Experiment: Do Wild Birds Feed in a More Wooded or Exposed Area?
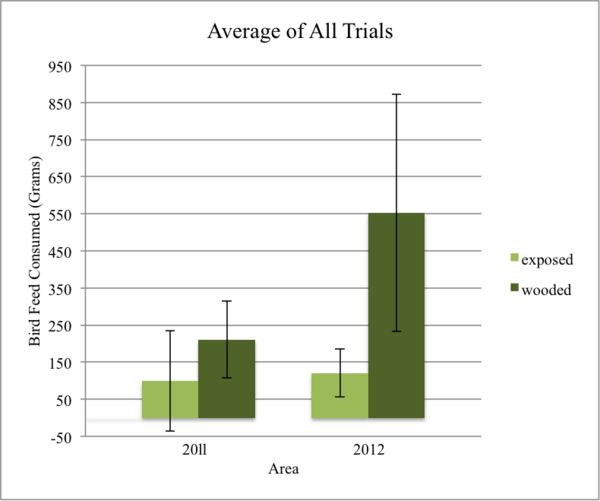
Habitat loss and global warming remain present-day issues that continue to place pressures on various ecosystems and their species. The authors of this paper performed studies over two years to understand whether birds feed more from wooded or exposed areas.
Read More...Analyzing resilience in a sample population as a novel qualifier for triage in psychological first aid

While serving as an immediate address for psychological safety and stability, psychological first aid (PFA) currently lacks the incorporation of triage. Without triage, patients cannot be prioritized in correspondence to condition severity that is often called for within emergency conditions. To disentangle the relevance of a potential triage system to PFA, the authors of this paper have developed a method to quantify resilience - a prominent predictor of the capability to recover from a disaster. With this resilience index, they have quantified resilience of differing age, race, and sex demographics to better inform the practice of PFA and potential demographic prioritization via a triage system.
Read More...Analysis of antibiotic resistance genes in publicly accessible Staphylococcus aureus genomes
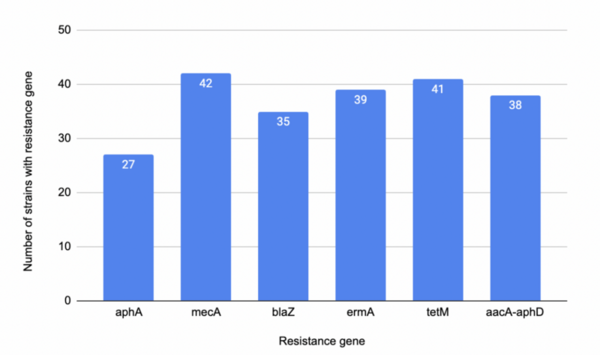
The authors looked at how the presence of difference antibiotic resistance genes would influence antibiotic resistance in Staphylococcus aureus.
Read More...Design and implementation of a cryptographically secure electronic voting infrastructure
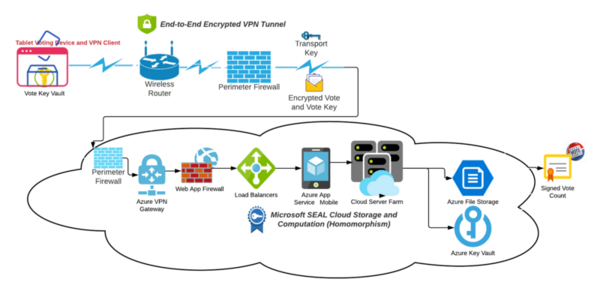
In this study, the authors present proposed cryptographic controls for election sites with the hypothesis that this will mitigate risk and remediate vulnerabilities.
Read More...Blockchain databases: Encrypted for efficient and secure NoSQL key-store
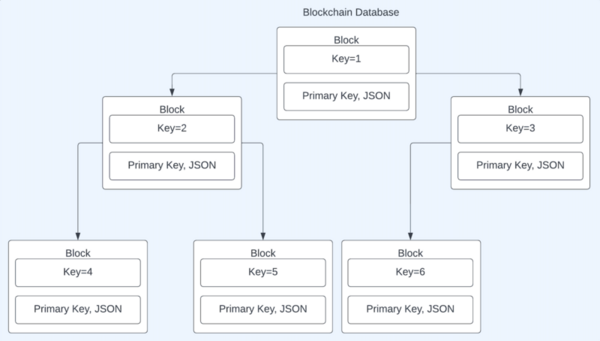
Although commonly associated with cryptocurrency, blockchains offer security that other databases could benefit from. These student authors tested a blockchain database framework, and by tracking runtime of four independent variables, they prove this framework is feasible for application.
Read More...