
Studying cut-resistant socks for hockey players
Read More...A systematic study of cut-resistant socks for hockey players
A comparison of starches and plasticizers for biopolymer synthesis and degradation
A potential enzymatic pathway for polystyrene degradation using saliva of greater wax moth Galleria mellonella
Investigation of the potential of waxworm saliva, the secretion of Galleria mellonella, for plastic degradation.
Read More...A 1D model of ultrasound waves for diagnosing of hepatomegaly and cirrhosis

The authors created a 1D model to diagnose hepatomegaly and cirrhosis via ultrasound of the liver.
Read More...A comparative study of food labels in the United States and India: Adherence to Codex Alimentarius guidelines
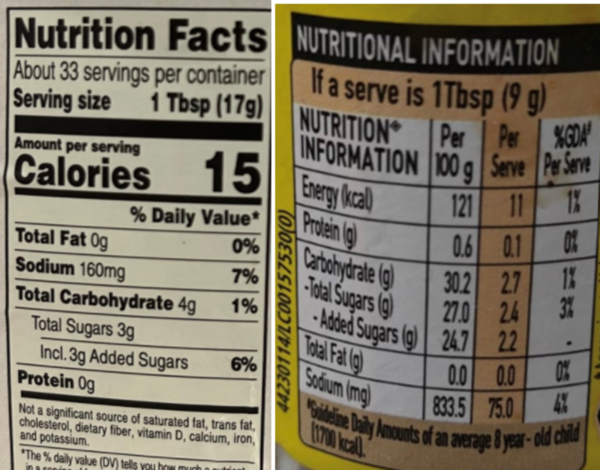
This study investigated how well food labels from 280 different brands across multiple food and drink categories in India and the US adhered to recommended nutritional labeling standards as outlined by the Codex Alimentarius.
Read More...A comparative analysis of machine learning approaches to predict brain tumors using MRI
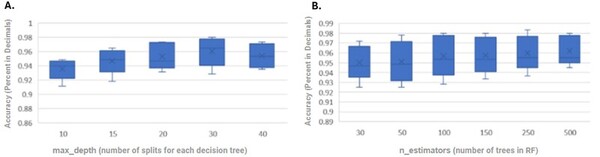
The authors use machine learning on MRI images of brain tissue to predict tumor onset as an avenue for early detection of brain cancer.
Read More...A low-cost method for purification of agricultural wastewater based on S. platensis
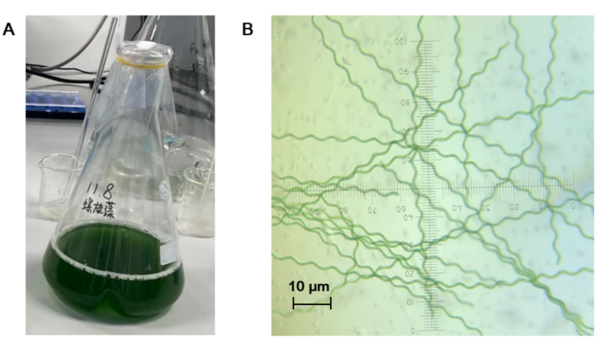
The authors looked at the ability of Spirulina platensis to reduce contaminants in wastewater in order to develop a more accessible treatment option. They found that S platensis did reduce the concentration of pollutants present within simulated agricultural wastewater.
Read More...A comparative study on the long-term effects of music and sports activities on cognitive skills of children
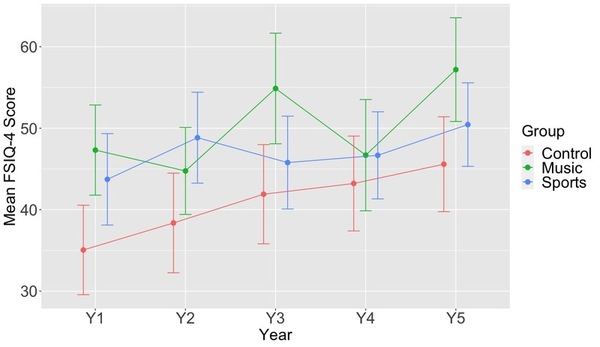
The study explores how music and sports impact cognitive development in young children, particularly in relation to learning disorders like ADHD and dyslexia.
Read More...A statistical analysis and generalized linear models of cerebral stroke
Here the authors sought to investigate whether and how cerebral stroke and other health-related variables are influenced together and amongst each other by using statistical analyses. Their analysis suggested relations between nearly all variables considered, with the strongest association between having heart disease and a cerebral stroke.
Read More...A natural language processing approach to skill identification in the job market
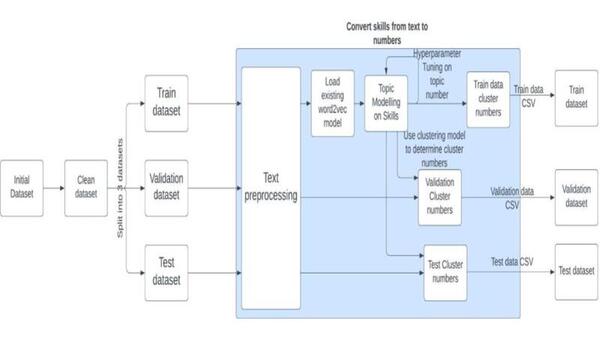
The authors looked at using machine learning to identify skills needed to apply for certain jobs, specifically looking at different techniques to parse apart the text. They found that Bidirectional Encoder Representation of Transforms (BERT) performed best.
Read More...